For anyone seriously interested in learning about network security or any of its related disciplines, you will eventually need to set up your own lab environment to gain valuable hands-on experience. This has been an integral part to my growth in the field, and I cannot stress the importance of it enough.
I followed Tony Robinson’s “Building Virtual Machine Labs” book to help me plan and set up this initial network. I highly recommend the book to anyone who may be interested in doing this themselves. (NOTE: at a minimum, you will probably want a computer with at least 4 cores and 16 GB of RAM). I’m using VMWare Esxi as my hypervisor, which is free to use for our purposes if you sign up for it.
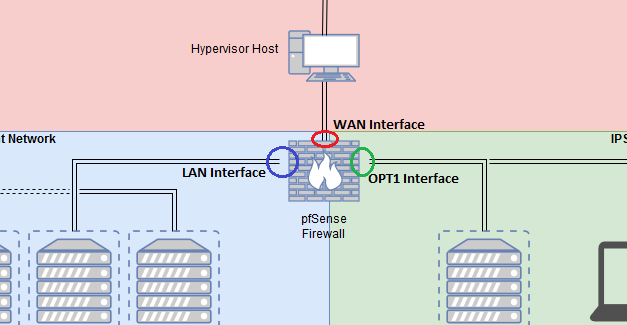
Here is the basic breakdown of it:

My Dell R710 server is the hypervisor host, seen in the red Bridged Network, which houses all the other virtual networks and machines.
Serving as the focal point of our network, we can see the pfSense Firewall sitting at the intersection of 3 networks. pfSense is actually much more than just a firewall, as it also serves as a fully-functional router and gateway to the Internet for our VMs.
In the blue Management Network section of the diagram, we have our SIEM (Security Information and Event Management) VM, running Splunk, and the management interface of our IPS (Intrusion Management Prevention) VM running Snort. Splunk gives us the ability to search, monitor, and analyze data that is fed to it by our IPS, all within a graphical web tool. Snort will monitor our network and perform real-time traffic analysis and packet logging. “Snort can can also be used to detect probes or attacks, including, but not limited to, operating system fingerprinting attempts, semantic URL attacks, buffer overflows, server message block probes, and stealth port scans.”
In the green IPS Network 1 section, you can see our Kali Linux VM from which we will be conducting our attack, and one interface of the IPS machine.
Finally, in the yellow IPS Network 2 section, we have an actual vulnerable VM, ‘Mercy’. This is connected to the second interface of our IPS VM.
(Note: This vulnerable VM can be easily swapped out for other vulnerable VMs that you may wish to practice on. Check of Vulnhub.com for more information!)
Now, the IPS will pick up all our ‘attacking’ traffic that will be sent from our Kali box to our vulnerable VM, and forward it to our SIEM for analysis!
The segmentation you see in the network is essential to keeping our home network secure from any malicious traffic that may be crawling around on the internal IPS networks. (This is especially important if you want to use your virtual lab to analyze malware)
Our pfSense firewall is where we configure the rules for the entire network. It has an fantastic web interface that allows managing the network to be easy and to-the-point
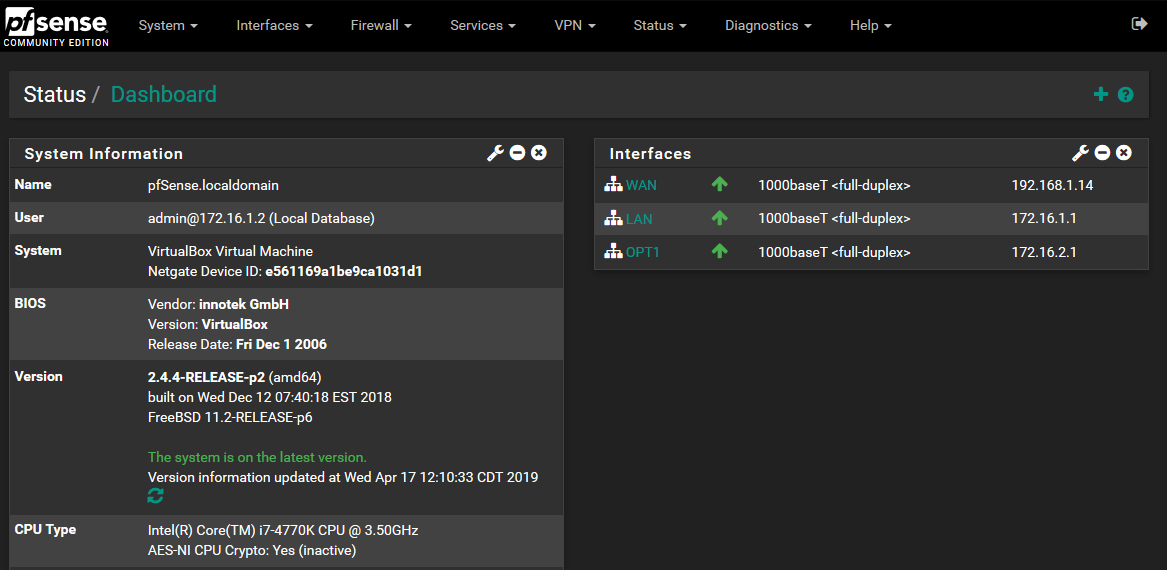
The picture above shows us the dashboard for the pfSense web management interface. It shows us high-level information such as the version number of the software, the hardware it is running on, and the interfaces we have configured.
Take note of the 3 interfaces I have configured here:
- WAN
- LAN
- OPT1
The WAN interface connects to our Bridged Network and is what points to the my hypervisor host (and eventually, the Internet)
The LAN interface connects to our Management Network and allows us to administer our SIEM and IPS from a trusted network segment.
The OPT1 interface connects to our IPS1 network, (and IPS2, via AFPACKET bridging from our IPS machine). The OPT1 interface is configured to be very restrictive of what traffic is allows in/out of the IPS network, as this is an untrusted network.
For those of you confused about AFPACKET bridging, I found Tony Robinson’s quick explanation of it helpful:
“AFPACKET bridging allows the two network interfaces of the IPS VM, connected to IPS1 and IPS2 networks to be fused together, allowing communication between the two network segments, so long as the IPS VM is powered on, and the… Snort IPS service is running. For instance, if you wanted your lab to serve as a malware analysis lab and wanted to ensure complete isolation to the internet. If you place your VMs in the IPS2 network, you could then turn off the IPS VM, or disable the… Snort service, and VMs in the IPS2 network have no external access to the internet or any other network segments (even the IPS1 network), whatsoever.”
Robinson, Tony (2017) Why All the Trouble? (AFPACKET Briding). Building Virtual Machine Labs, 32.