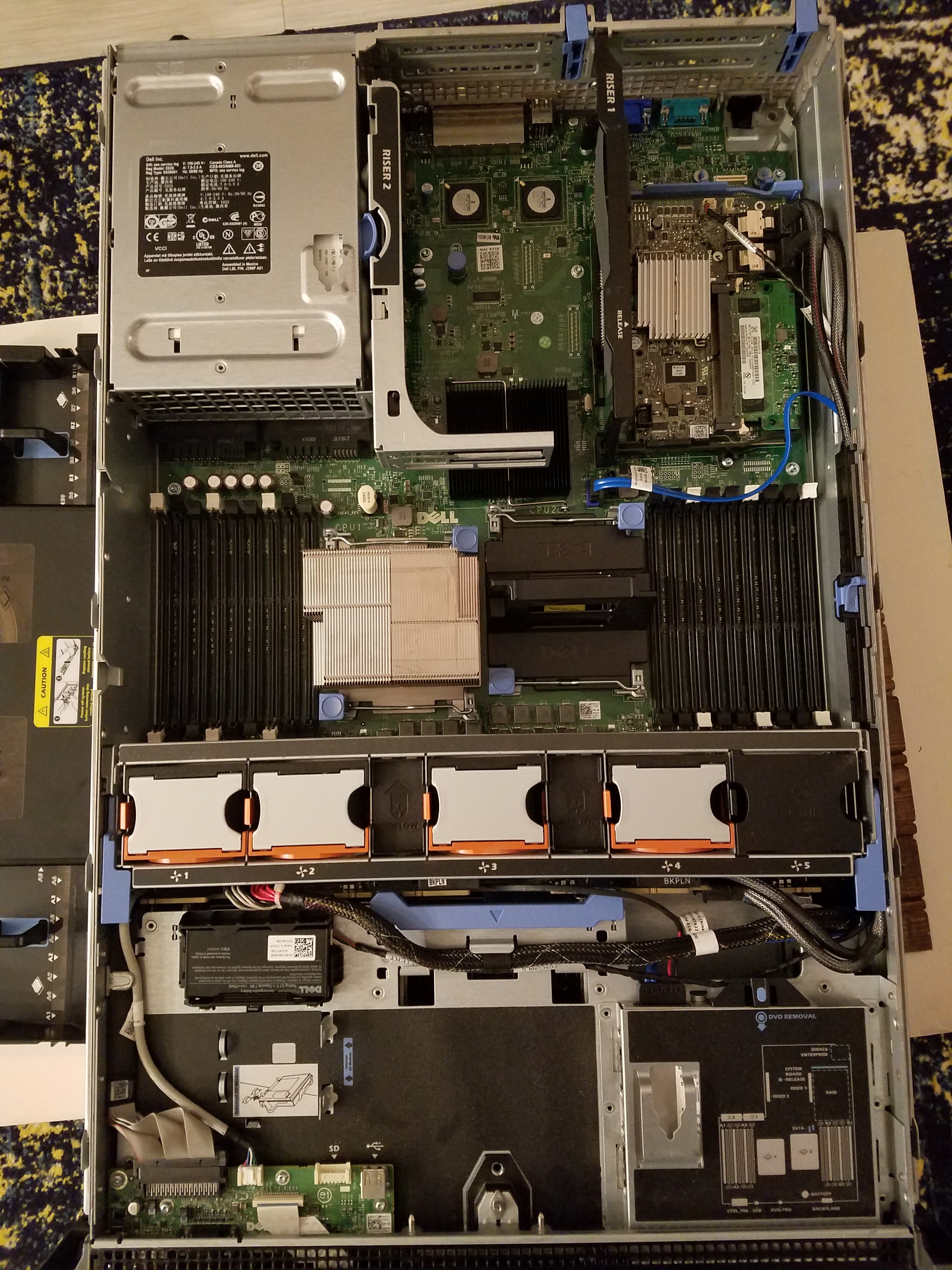
So I finally made the plunge and purchased some actual hardware for my home lab environment. I was able to find a great deal on a used Dell R710 server from someone at my local security meetup group. It was pretty bare from a specs standpoint when I first got my hands on it (only containing 12 GB of RAM, no hard drives, and a single Xeon E5630 CPU clocked at 2.53 GHz).

Naturally my first order of business was to procure some of the missing components, and beef up the RAM a bit. Since I’m planning on primarily using this server as a virtualized lab environment, I wanted a minimum of 32 GB of RAM, and an SSD for the faster IOPS. I settled with a modest 500GB Samsung 860 EVO for my first disk. But the R710 has 6 total drive bays for expansion as I see fit.
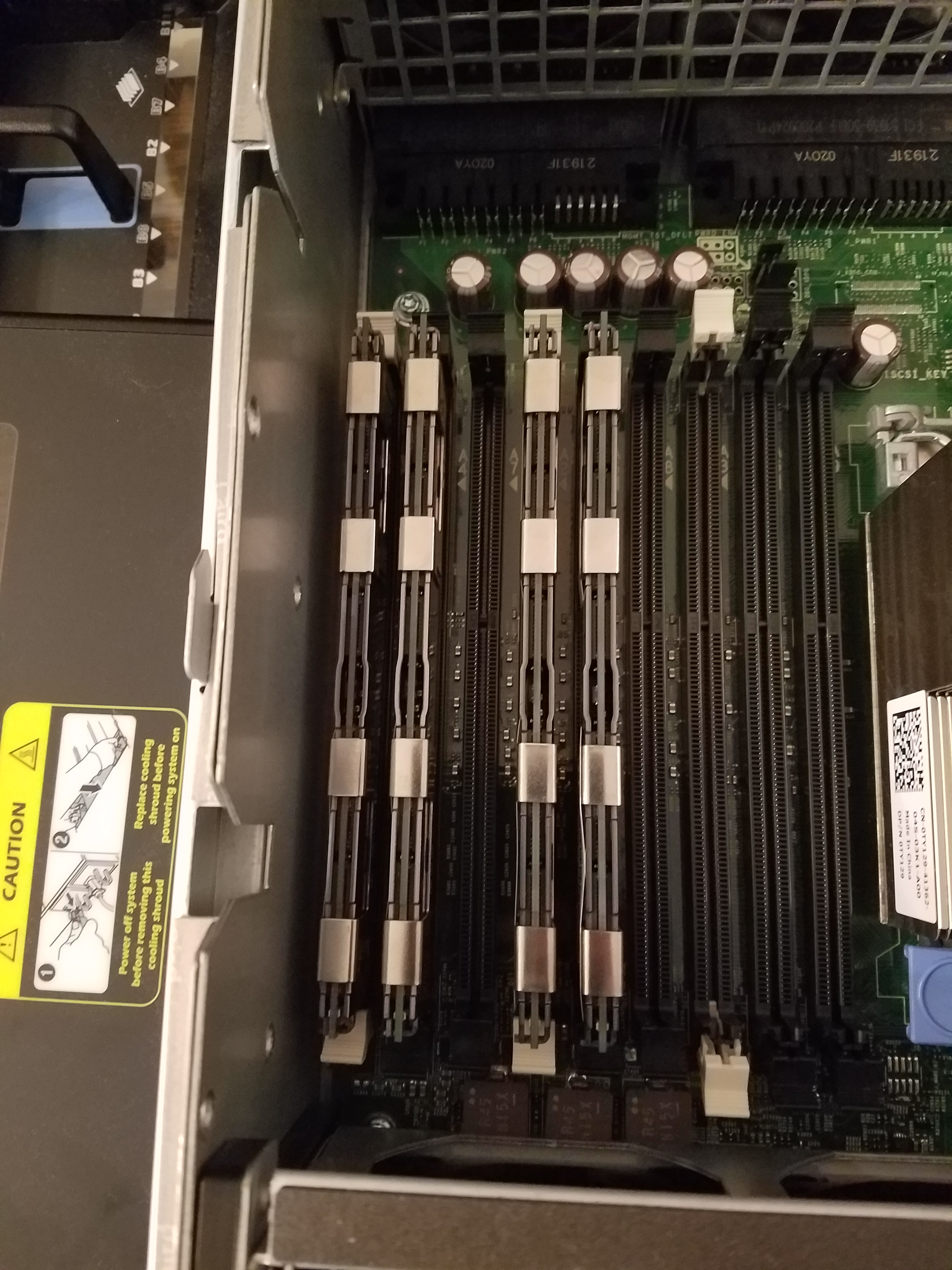
I purchased four 8GB sticks of RAM off eBay. Taking care to make sure it was compatible with the server.

The 6 blue sticks at the top of the picture was the previous owner’s RAM. But they were only 2 GB UDIMMs. The memory I purchased was RDIMM, and the two are not compatible in the same machine, so I had to pull them from the server.
Now, there is a specific way you need to organize your RAM in order to optimize your system. Dell provides easy to follow documentation in this regard. Taking a look at the following diagram, it instructed me on which slots I needed to fill with my RAM:

Since my server has a single processor, and I have 4 8GB sticks of RAM (for a total of 32GB), I need to fill memory sockets 1, 2, 4, and 5. The next picture breaks down which slot is which:

As mentioned previously, I only have 1 CPU, so we can ignore the right side of the image.
Armed with this knowledge, I simply inserted the RAM in as shown below:
Once the RAM was installed, I mounted the SSD into the first drive bay. As you can see from the picture below, this bay was clearly meant to house a larger, mechanical hard drive, but mounting the SSD into the side works just fine.

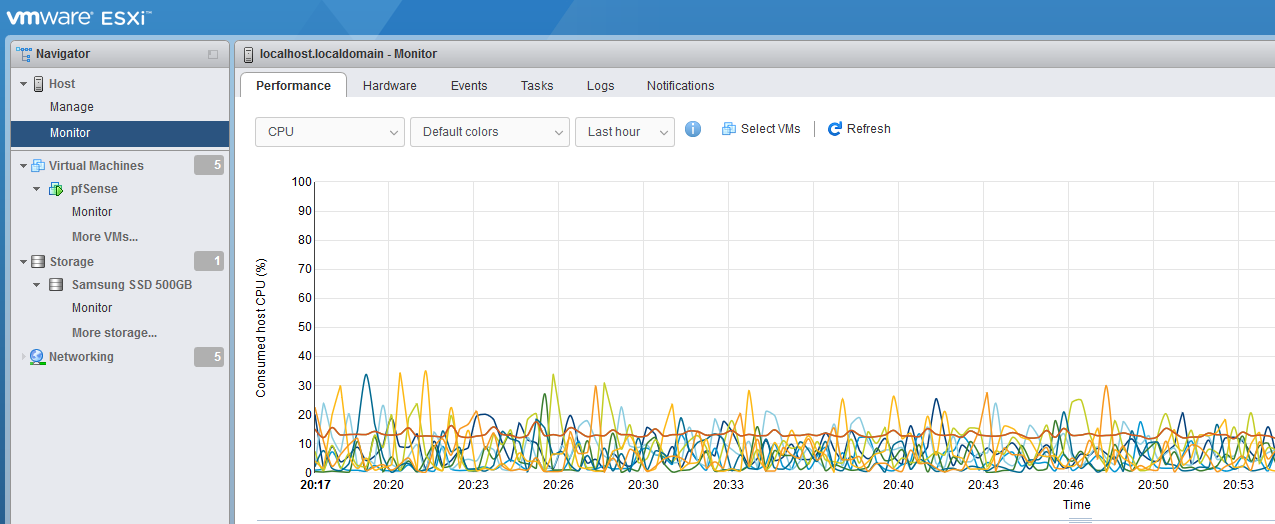
Next, I needed to get a hypervisor installed on to the machine. I chose to go with VMware’s ESXI hypervisor. Using Rufus, I created a bootable USB with the ESXI ISO file on it, and booted the server into it. Despite it’s age, this guide still works great for configuring the USB.
The installation process for it is pretty self explanatory and easy to follow. You simply have to enter the boot settings at startup and tell the server to use the USB as its primary boot device. (Pro tip: make sure you have a BASIC keyboard… I found out the hard way that my Corsair mechanical keyboard was not recognized by the R710’s BIOS, and had to order a cheap keyboard off Amazon just for the initial installation…)
Once ESXI was installed onto the server, remote management is simple with the web-based GUI. Simply navigate to the IP address that your server has been assigned in your favorite web browser. By the way, I statically assigned my server’s IP address, so I could simply bookmark the web interface and not have to worry about it constantly changing IP’s.
Provisioning a VM in ESXI is as simple as clicking the ‘Create / Register VM’ button, and running through the configuration steps. You can easily upload ISO files from your desktop computer to the server through this web interface as well, which is very handy.
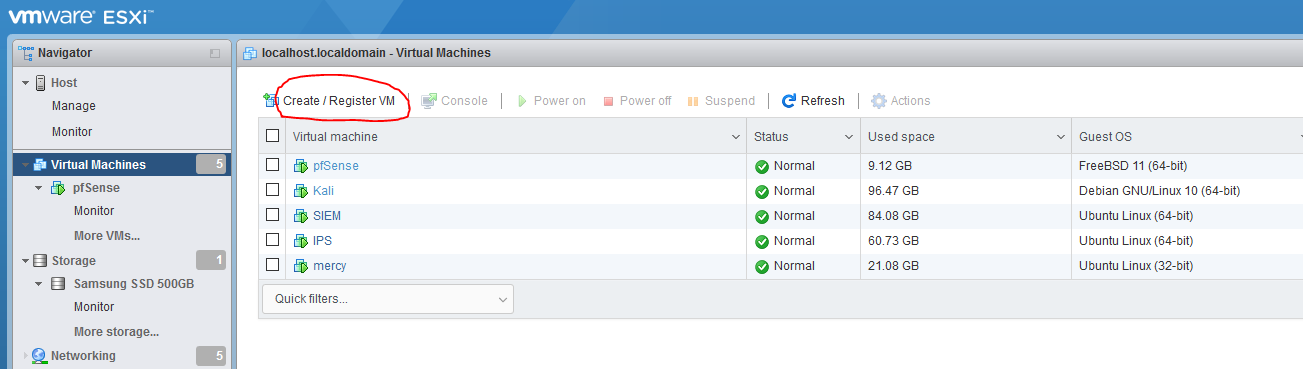
For information on how I created and segmented the virtual network, check out my post on “My Virtual Lab Environment”. Configuring your network settings is easily done via the ‘Networking’ tab in ESXI. Here you can see I’ve created 5 virtual switches.
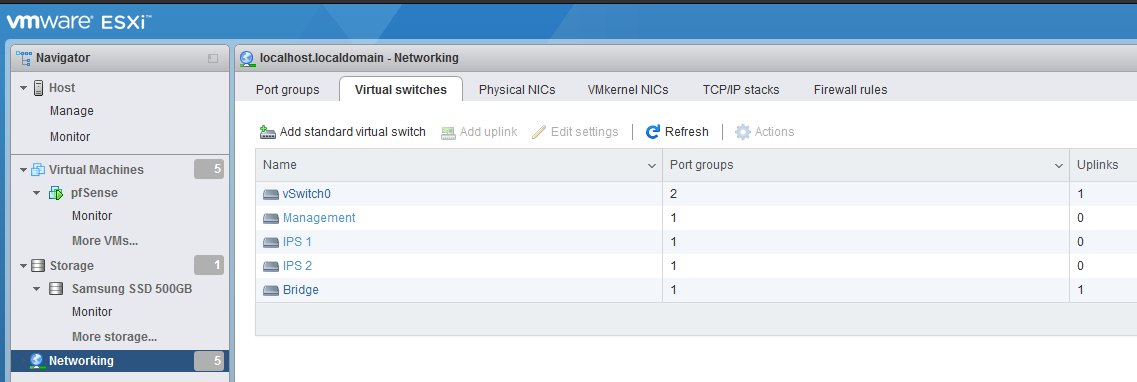
(‘vSwitch0 ‘comes pre-configured, and is what allows us to connect from our remote desktop to the server. It essentially binds the physical NIC on the server to the virtual NIC that ESXI manages.)
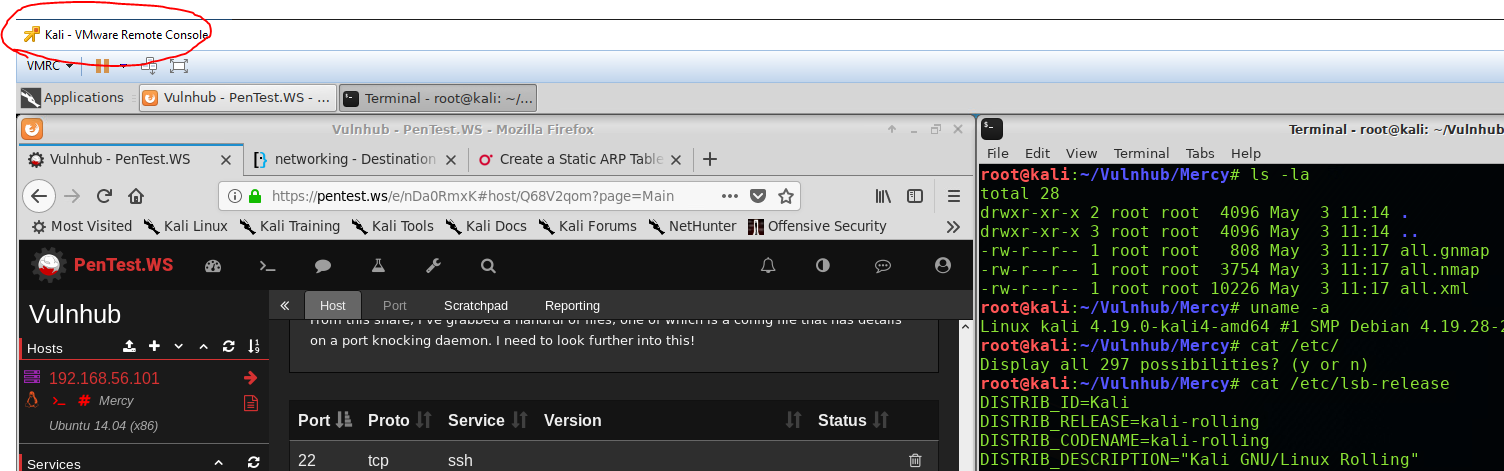
To access your VMs, ESXI provides a remote console interface, that allows you to set up your machines initially or log into their desktops:
And that’s all there was to it. I now have a scalable lab environment, with tons of room to grow and build upon. In the future, I’d like to build out an Active Directory environment, to have a more realistic ‘enterprise’ network to play with and learn from. Hopefully that will be coming in the near future, so stay tuned for it everyone. Thanks for reading, and happy hacking.